Version 11.2¶
11.2.14¶
Public Key Infrastructure¶
We have implemented AIA Chasing . Our certificate management system now automatically handles "incomplete" certificate uploads. If a certificate is uploaded without its required intermediate bundle, the system will attempt to download the missing links from the issuing Certificate Authority to automatically complete and validate the chain of trust.

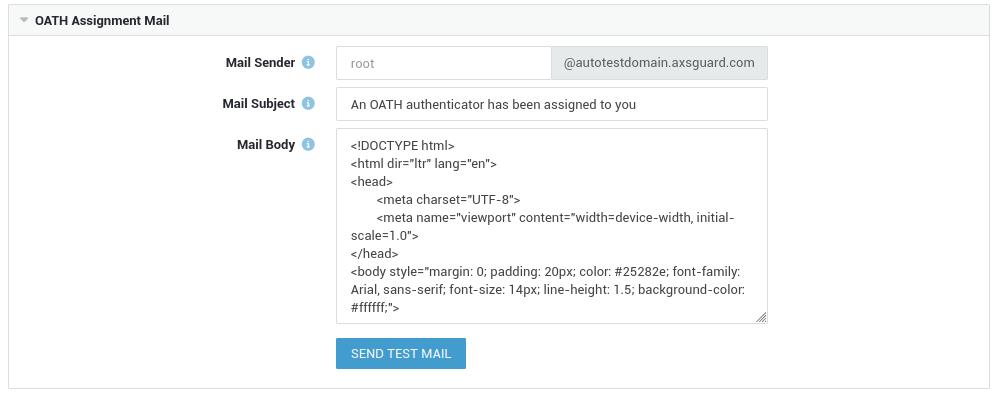
OATH Notifications¶
We’ve introduced granular controls for OATH assignment notifications, allowing you to configure a custom email sender, subject, and message body.
The message body supports full HTML, making it easy to deliver branded onboarding instructions for OATH authentication. To simplify deployment, an integrated testing tool is included to validate the outgoing email configuration and ensure the template renders correctly across different email clients.
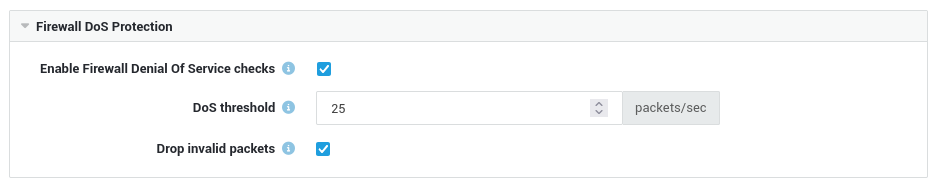
Firewall Configuration¶
The firewall now automatically drops invalid packets, including those resulting from network anomalies or specially crafted stealth scans. These events are logged with the reason BAD2: invalid packet.
This option is enabled by default and can be disabled by navigating to Firewall > Limits.
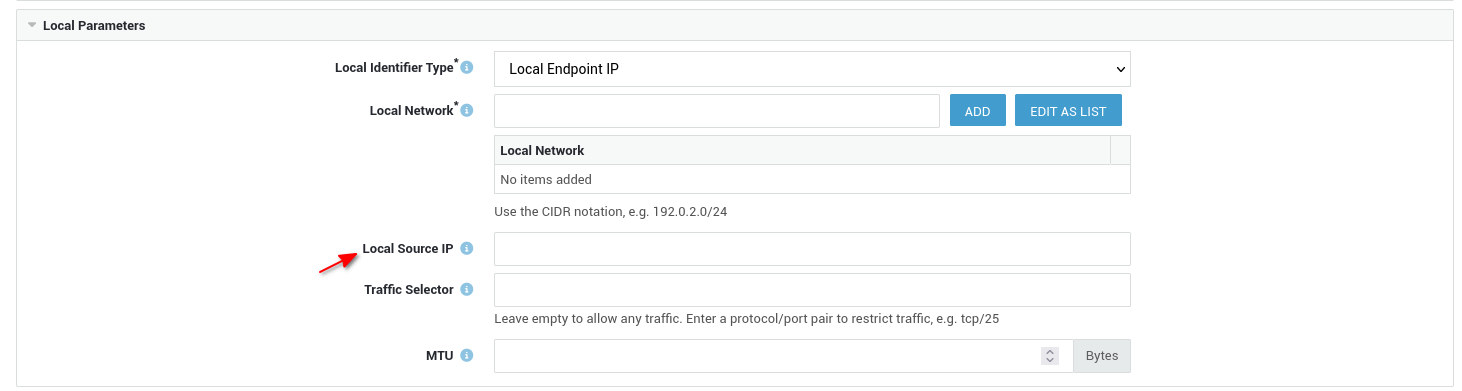
IPsec Configuration¶
- We resolved rendering issues that occurred when sorting IPsec tunnels by status.
- System administrators can now specify the source IP address used by the appliance for traffic sent through an IPsec tunnel.
System Enhancements¶
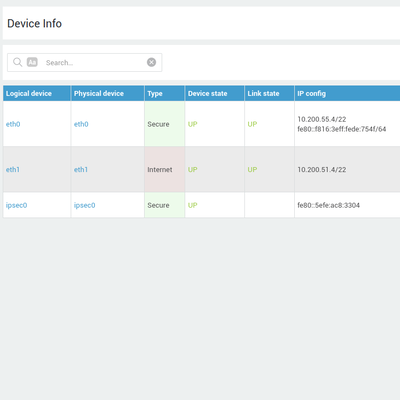
- Removed the need for a system reboot after changing the MAC address or MTU of a network device.
- Reports: Include the current day when selecting 'this week' and 'this month'.
- Our company logo has been updated across the configuration tool.
- Fixed an issue where FQDN-based firewall rules would intermittently lose their resolved IP addresses every two hours.
- The
fwd-edrfirewall rule has been updated to reflect our current EDR offering. - Improved disk size validation for new virtual appliance installations.
- Allow DS sync profiles to be enabled when a specific domain is configured.
- User synchronization: Fixed an issue where invalid or corrupted data could cause user accounts to be incorrectly disabled or deleted.
- DNS agents now correctly recognize the AXS Guard appliance as a SecureDNS server when the feature is enabled.
- SMTP authentication can now also be configured for forwarded domains.
11.2.13¶
Personal AXS Guard¶
Introduced support for the new PAX Industrial AGi200. This model is now available for selection in the configuration tool.

System Enhancements¶
- Updated various packages to keep the base system secure.
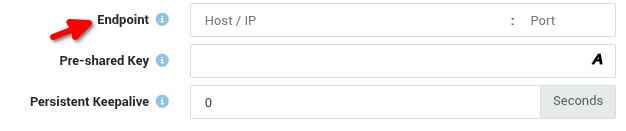
-
Improved the host:port endpoint field on the WireGuard peer page to make it more intuitive.
-
In the reverse proxy, URLs in response headers are now rewritten to avoid exposing back-end hostnames.
- Removed the need to reboot after changing connectivity check settings.
- Renamed Protection Pack to Threat Intelligence Pack.
11.2.12¶
Migration to CoreDNS¶
Adopting CoreDNS consolidates multiple DNS services into a unified architecture, reducing overall network complexity. This change is internal and does not require any action or configuration changes from system administrators.
CoreDNS is built on a modern, memory-safe foundation and natively supports encrypted protocols such as DNS-over-HTTPS, ensuring that DNS traffic remains private and secure.
This change delivers a more reliable, future-proof DNS environment that is easier to maintain and faster to scale.
11.2.11¶
WireGuard¶
WireGuard is now available on AXS Guard, offering a high-performance alternative to IPsec and OpenVPN. Our implementation supports both Client-to-Site (C2S) and Site-to-Site (S2S) configurations, ensuring high-speed, state-of-the-art encrypted connectivity for remote users and branch offices alike.

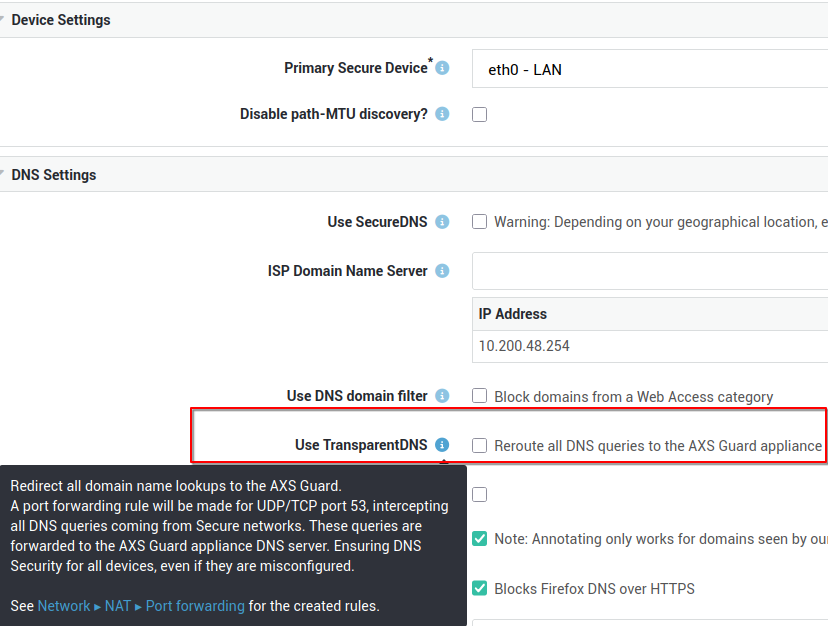
Transparent DNS¶
We’ve introduced Transparent DNS. When enabled, all DNS queries are automatically rerouted through AXS Guard. This ensures consistent DNS security across all devices, even those with manual or incorrect configurations.
To enable this option, log in to your appliance and navigate to Network > General.
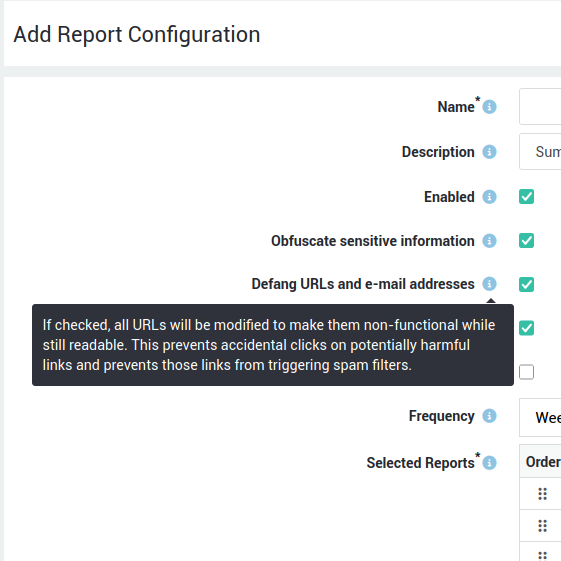
Threat Reports¶
Added support for domain defanging in reports. This eliminates the risk of accidental interaction with potentially harmful URLs and prevents clicks from triggering spam filters. This option can be enabled under Reports > Configuration.
System Enhancements¶
- Public DNS: Use
ip6:prefix in SPF records when the configured IP address is not IPv4. - Improve matching for overlapping user authentication restrictions.
-
Lists are now also visible in the firewall rule overviews (Towards, Through & DMZ filter).

-
Allow the configuration of DCO in OpenVPN on appliances that have CPUs without AES-NI support.
- Remove the consecutive-character check from password validation.
- Make new appliances available faster on AXS Guard Cloud during initial setup.
- LDAP: no longer synchronize users belonging to groups that are unknown to the appliance.
- Increase the spam score of emails that have been flagged by SecureDNS.
- Skip annotating queued emails with the subject when the queue takes too long to load.
- Allow the use of keyboard shortcuts on the reverse proxy login page.
- Reinforce SSH security by disabling challenge-response authentication.
11.2.10¶
OpenVPN¶
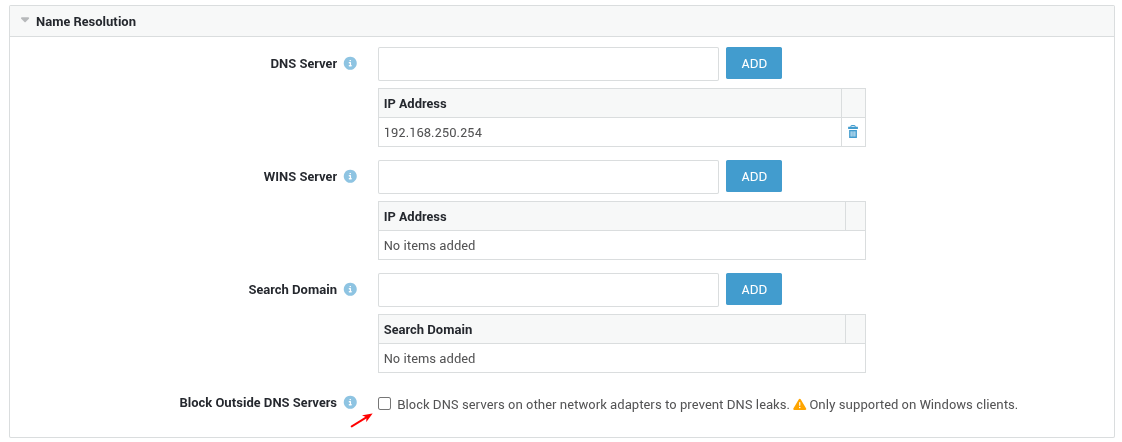
DNS Leak Prevention¶
Block Outside DNS Servers: This option allows system administrators to block all outbound DNS traffic (UDP and TCP on port 53) originating from network adapters other than the client's OpenVPN tunnel adapter, thereby preventing DNS leaks. This feature is supported on Windows clients only. To enable this option, navigate to VPN > OpenVPN > Server and select the Push-to-Client Configuration tab.
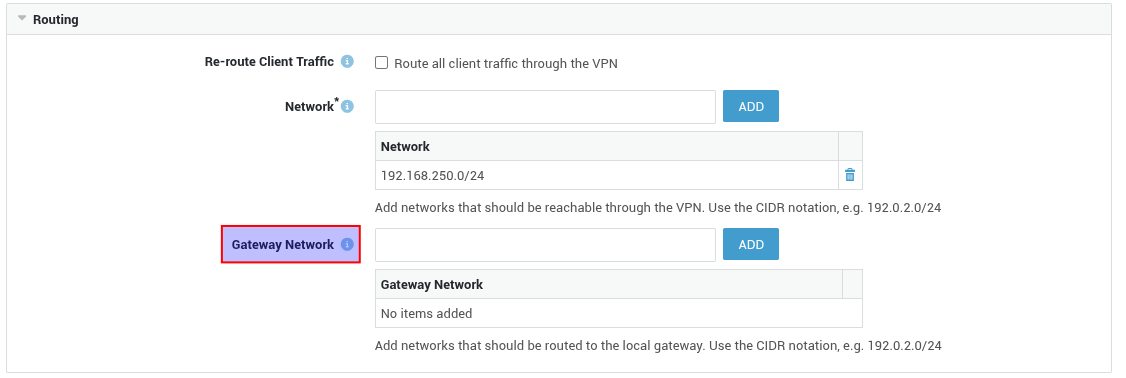
Split Routing¶
Gateway Network: This Push-to-Client feature allows system administrators to add networks that must be routed through the client’s existing default gateway. This is the opposite of the Network option, where traffic is always routed via the OpenVPN tunnel. Add the network(s) that must be reachable via the client’s default gateway, using the CIDR notation (e.g., 192.0.2.0/24).
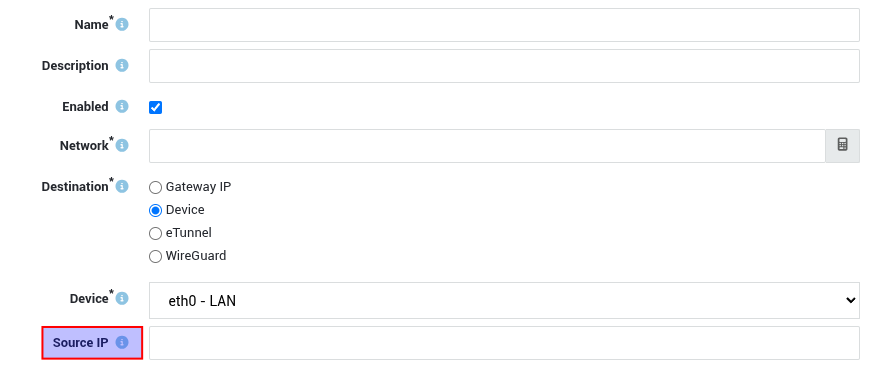
Routing¶
When routing traffic via an AXS Guard network device that has multiple IP addresses, system administrators can control exactly which IP address should be used as the source for that traffic. This feature allows the configuration of the preferred source IP address based on the route's destination.
System Enhancements¶
- Improved menu search algorithm
- Allow system administrators to change the DNS name of network devices
- Improve DHCP server validation to prevent invalid configurations
- Hide dashboard widgets for disabled features
- Update the default QRadar firewall rule
11.2.9¶
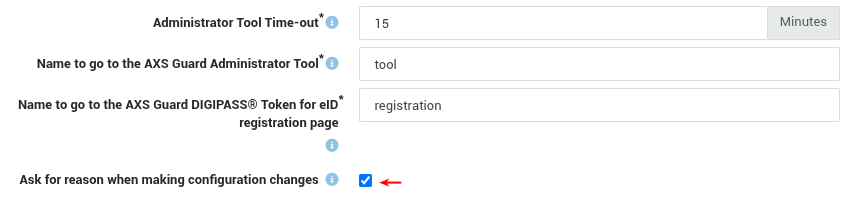
Change Management¶
Recording a reason for every configuration change is an essential practice to ensure compliance with cybersecurity regulations such as ISO 27001 and NIS2. Providing a clear reason supports accountability and security: identifying who initiated the change, risk mitigation, understanding potential impacts and troubleshooting.
- Log in to your AXS Guard firewall.
- Navigate to System > Administrator Tool.
-
Enable Ask for reason when making configuration changes and save your settings.
Firewall Enhancements¶
We improved the user experience of the firewall logging and rule overview pages:
- Devices in rule overview and log pages are now clickable.
- We replaced
+and–symbols with icons for included and excluded IP ranges. - Added port & service information.
-
Anyis now greyed out for better readability.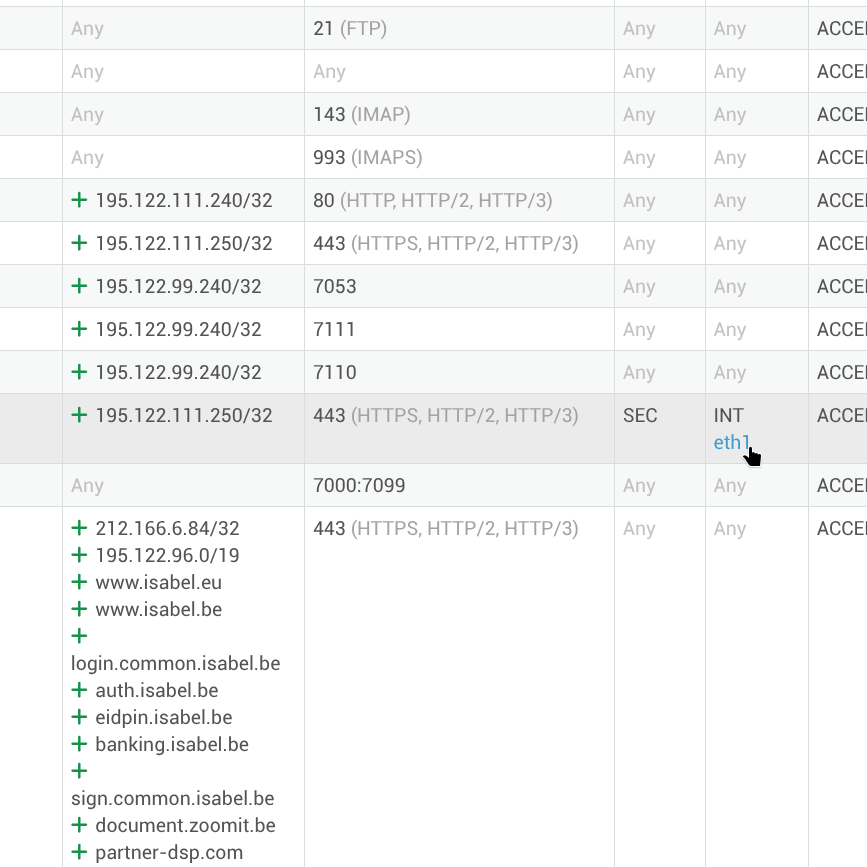
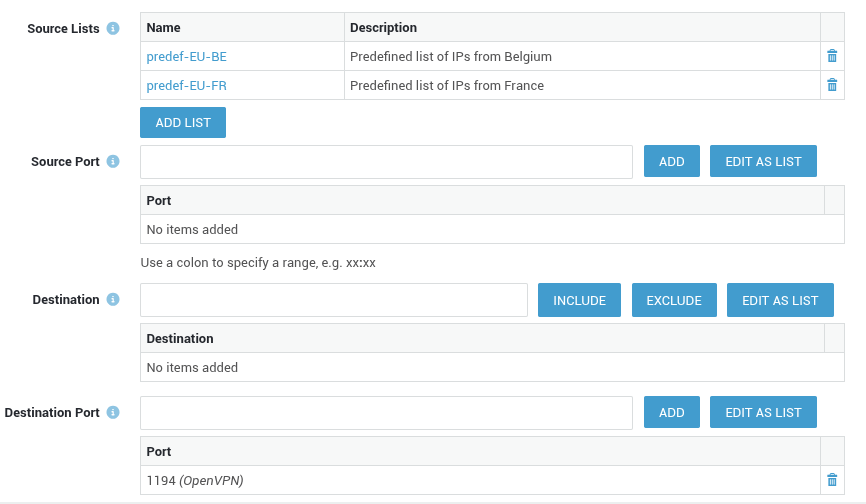
GeoIP Filtering¶
You can now use GeoIP lists as a source filter in firewall and port forwarding rules.
This enables administrators to create specific ACCEPT rules to override the global GeoIP configuration, giving organizations much finer control over access to particular AXS Guard services or specific network resources.
Security Updates¶
- CVE-2025-9230: Update OpenSSL to fix out-of-bounds read and/or write while decrypting CMS messages.
- CVE-2025-9096: Update
curlto fix out-of-bounds read for cookie path. - CVE-2025-40928: Update perl
JSON::XSto fix integer buffer overflow leading to segmentation faults. - CVE-2025-59375: Update
expatto fix large dynamic memory allocations via small XML documents.
Bug Fixes¶
- Show the domain field when configuring Entra ID profiles with the Basic bundle.
- Fix export of OpenVPN client configurations for Entra ID in hybrid and cloud-only setups.
- Fix rendering of the Application Control detailed page.
- Fix FQDN resolution for port forward rules.
- Fix export in overview pages when data contains HTML.
- Fix caching of referred data objects for improved loading speed.
11.2.8¶
Bug Fixes¶
- Updating user details without changing the password no longer flags the password as insecure.
- High Availability: Fixed a problem that caused the firewall to become overly restrictive following a reboot.
11.2.7¶
Configuration Tool¶
- We've updated the user password complexity requirements. Passwords must now be at least 12 characters long.
- Added a confirmation step when releasing spam messages.
- Fixed an issue with the visibility of the Last Used field on the certificate overview page.
- Corrected the escaping of field values when exporting overview pages.
- Resolved an issue with the import of ECC certificates.
Mail System¶
- Spam checks now follow page redirects to enhance DNS security.
- Domains are now checked against Dynamic DNS domain lists.
- The spam filtering engine is now automatically trained to recognize released spam messages as "ham".
11.2.6¶
Configuration Tool¶
Drag & Drop¶
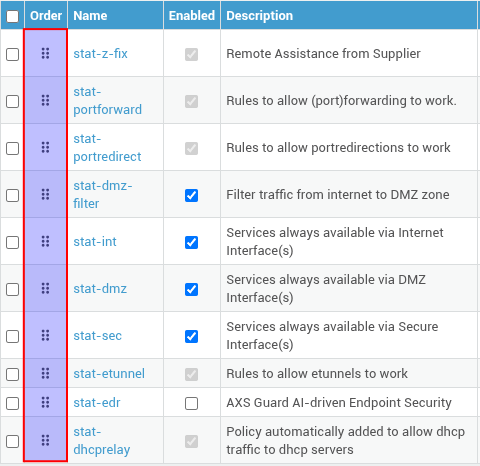
The following overview pages now support drag-and-drop ordering:
- Static firewall policies
- Internet redundancy filters
- NAT configuration pages
This enhancement allows system administrators to easily reorder entries.
Internet Redundancy¶
We improved the Internet Redundancy filter validation to prevent invalid or non-functional configurations.
OpenVPN¶
For OpenVPN servers with web authentication enabled, the user's sync source is now taken into account when exporting ovpn configuration files. This ensures that local authentication is only enforced on the client when required, delivering a seamless user experience in hybrid authentication environments.
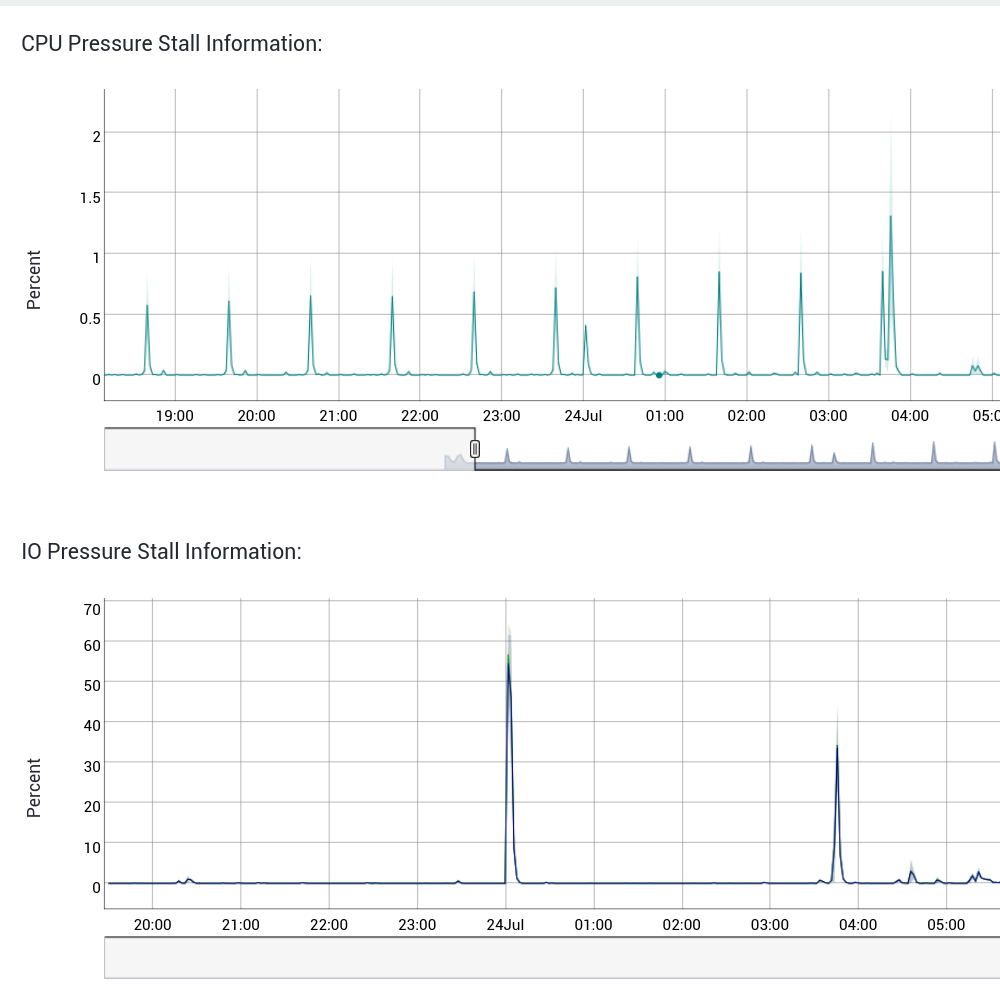
Statistics¶
Additional statistics have been added to improve appliance monitoring and accelerate troubleshooting.
- PSI (Pressure Stall Information) is now available to identify when and where resource bottlenecks (stalls) occur.
- For disk monitoring, detailed timing metrics and queue size data are now included.
11.2.5¶
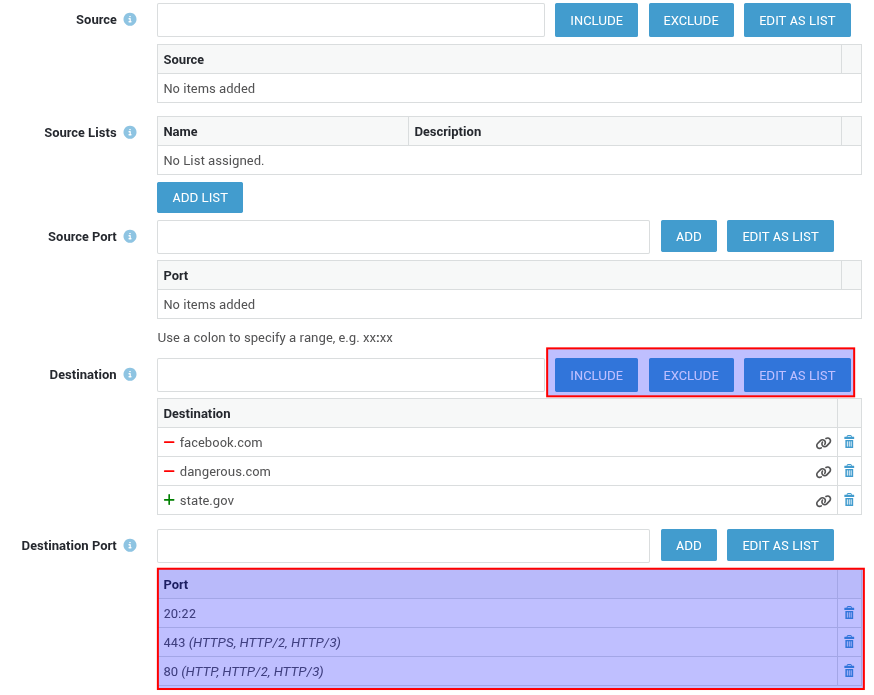
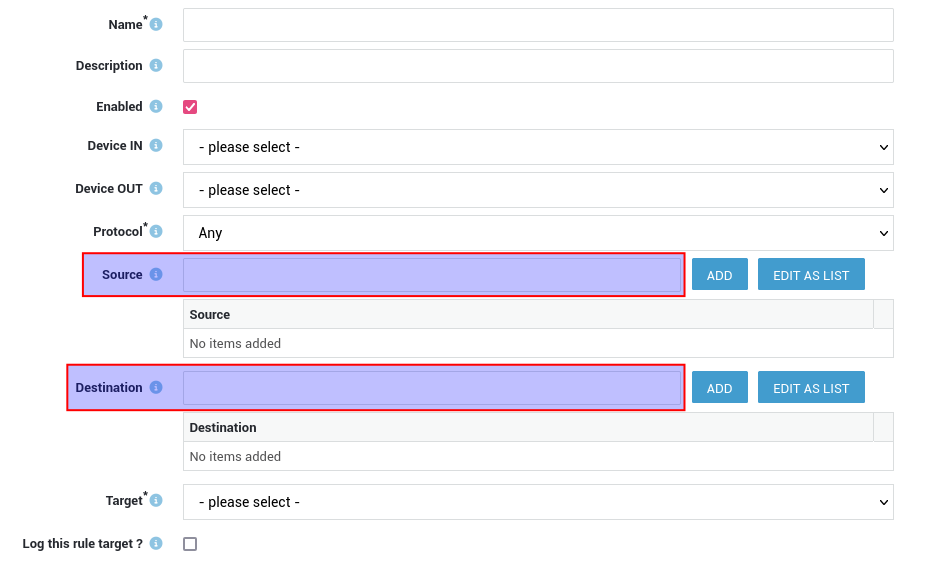
Firewall Rules¶
We've improved the firewall rule configuration interface, making it easier and more efficient to manage your network security:
-
Multi-Device Selection: Create firewall rules that apply to multiple devices at once.
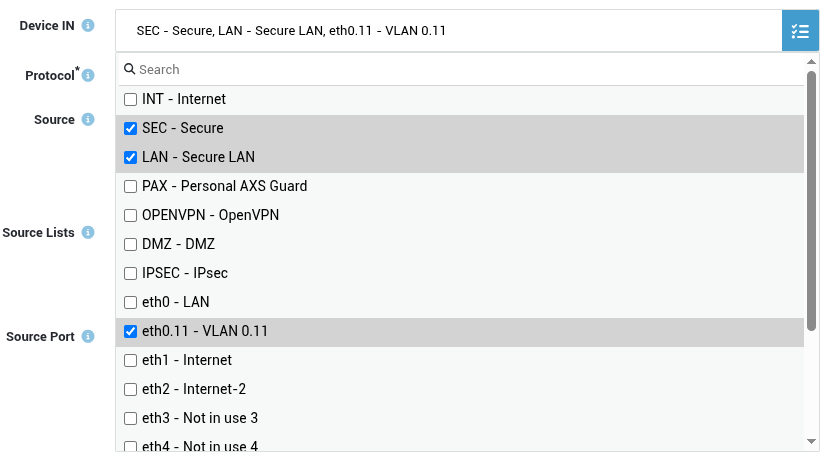
-
Support for Multiple Ports and Port Ranges: Configure multiple source and destination ports or port ranges within a single rule.
-
Source and Destination Exclusion: Easily exclude specific sources or destinations from a rule for more precise network access control.
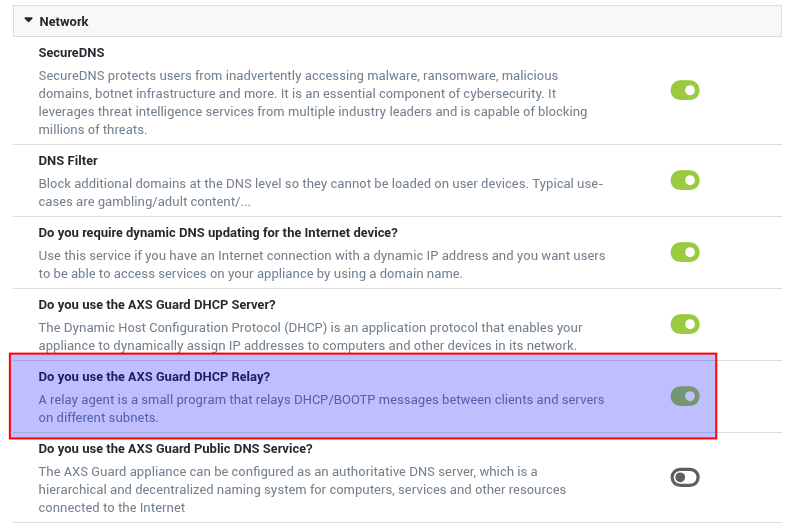
DHCP Relay¶
We're introducing the DHCP Relay service, which enables DHCP requests to be forwarded between different networks. This is especially useful when an external DHCP server is located on one subnet but needs to provide IP addresses to devices on another.
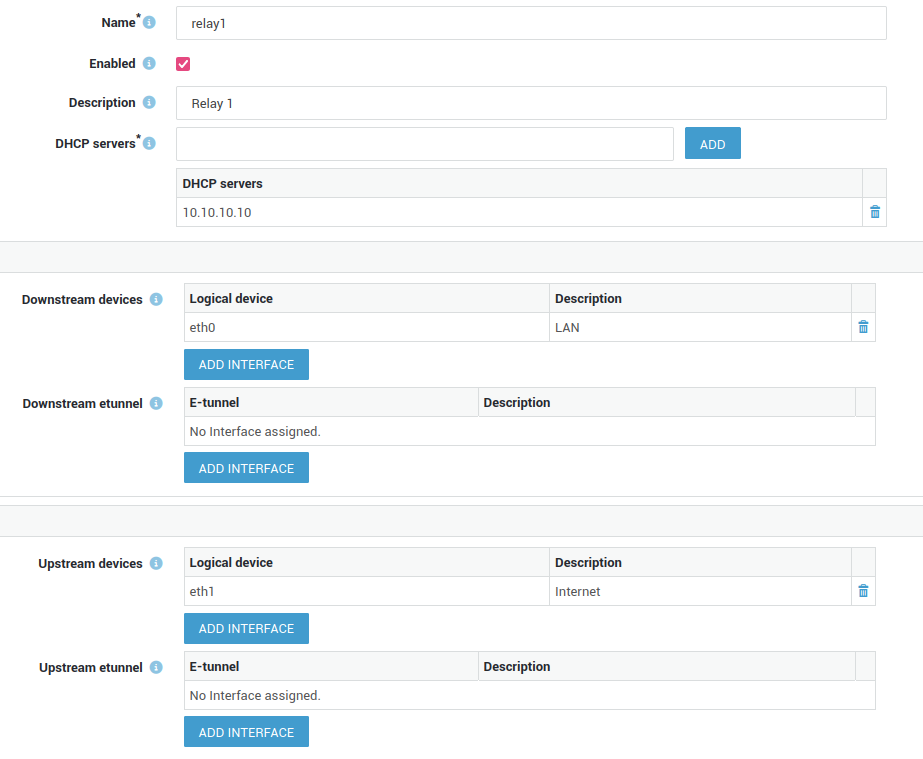
You can enable this feature from the Feature Activation page under the Network tab.
11.2.4¶
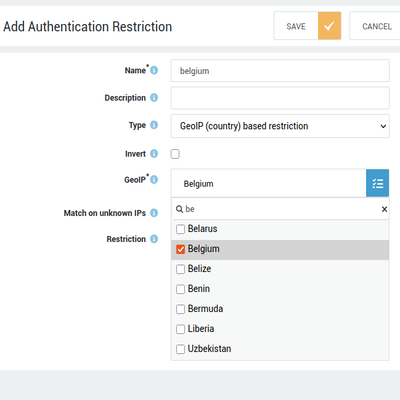
User Authentication¶
- Added support for country-based authentication restrictions.
-
User authentication can now be allowed or blocked based on geographic location.
Firewall Rules¶
- Added the option to filter traffic based on geographic location.
-
Blocking network traffic to and from specific countries or regions can significantly reduce the attack surface.
Configuration Tool¶
- Device status page: You can now filter on device type.
-
The process groups on the statistics page are now sorted.
Miscellaneous¶
- Entra ID sync now converts all usernames to lowercase.
- Decreased the timeout for directory services synchronization.
- Added the "friendly name" attribute to OpenVPN certificates for Windows 11 clients.
- SecureDNS: Emails matching a botnet or APT signature are now quarantined for review.
- Enhanced mail whitelisting capabilities.
11.2.3¶
Firewall Enhancements¶
- Outdated DNS query results are no longer retained in firewall rules.
- Resolved a race condition when loading combinations of FQDN-based and static rules.
- Firewall rules associated with non-existent devices now correctly fail to match network traffic.
- Enhanced the synchronization mechanism for cloud-based firewall rules.
Bug Fixes¶
- Updated multiple software packages to remediate recent CVEs.
- Improved email scanning capabilities to inspect additional headers for known malicious domains.
- Fixed a race condition that could cause DNS server failures when OpenVPN was misconfigured.
11.2.2¶
Bug Fixes¶
- Fixed an issue where the source exclude fields in firewall and port redirection rules were missing from system backups.
- Addressed an issue in the DKIM signing service that could lead to the blocking or flagging of legitimate emails.
- Resolved an issue that limited the maximum number of users allowed in authentication restrictions.
- Ensure that user and group authentication restrictions are correctly enforced after creation or modification.
11.2.1¶
Bug Fixes¶
- Improve connection stability towards AXS Guard cloud.
- Reconfigure VLAN devices when an IP alias changes.
- Remove unwanted security event errors related to statistics gathering.
- Correctly handle specific output device usage in firewall rules.
11.2.0¶
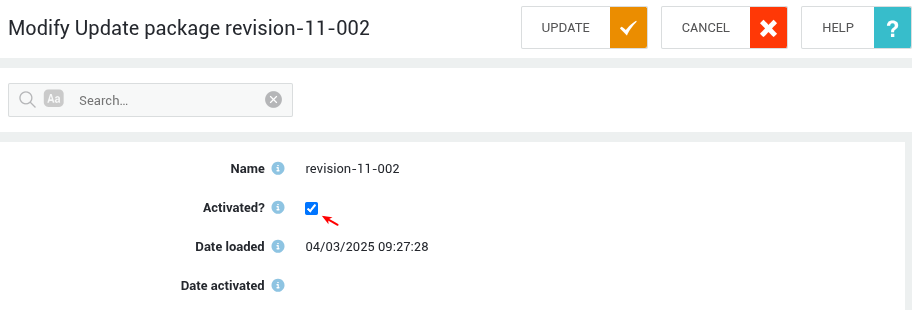
This document provides crucial information regarding the upgrade to AXS Guard version 11.2.0. Please review it carefully to ensure a smooth transition and prevent service disruptions.

Timing & Considerations¶
- The upgrade process is estimated to take approximately 30 minutes.
- To minimize service interruptions, we strongly recommend to schedule this upgrade during off-peak hours or a designated maintenance window.
- Please communicate this scheduled downtime to your users in advance.
- During the upgrade, the system will be temporarily unavailable.
-
Go to Software Updates > Software Packages to install the new version.
Key Feature Enhancements¶
UEFI Support¶
- AXS Guard now supports Unified Extensible Firmware Interface (UEFI) boot.
- This modern standard offers improved security, faster startup times, and enhanced compatibility with newer hardware.
- This transition eliminates reliance on legacy BIOS boot and enables installation on UEFI-enabled virtual machines using a virtual CD or USB drive.
- For new virtual installations, configuring UEFI boot is highly recommended.
- If you already have an existing installation, a fresh installation is required to enable UEFI support.
Firewall Rule FQDN Support¶
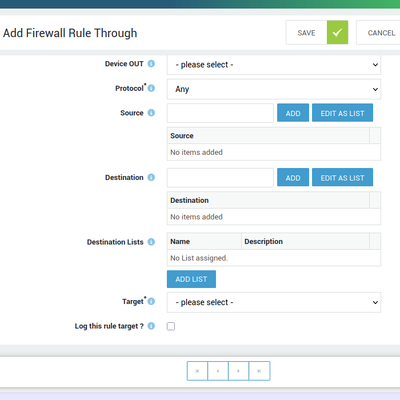
We enhanced FQDN support for firewall rules, which offers greater flexibility and control over network traffic. Enhancements include:
- FQDN support for DMZ filter rules, simplifying access management for servers in your DMZ.
- FQDN support for port forwards, streamlining traffic forwarding to internal servers based on domain names.
- FQDNs can be used as both the source and destination in "towards" rules, allowing granular control over traffic originating from or directed to specific domains.
- FQDNs can be used as both the source and destination in "through" rules, enabling precise filtering of traffic passing through the firewall based on domain names.
Mail System Enhancements¶
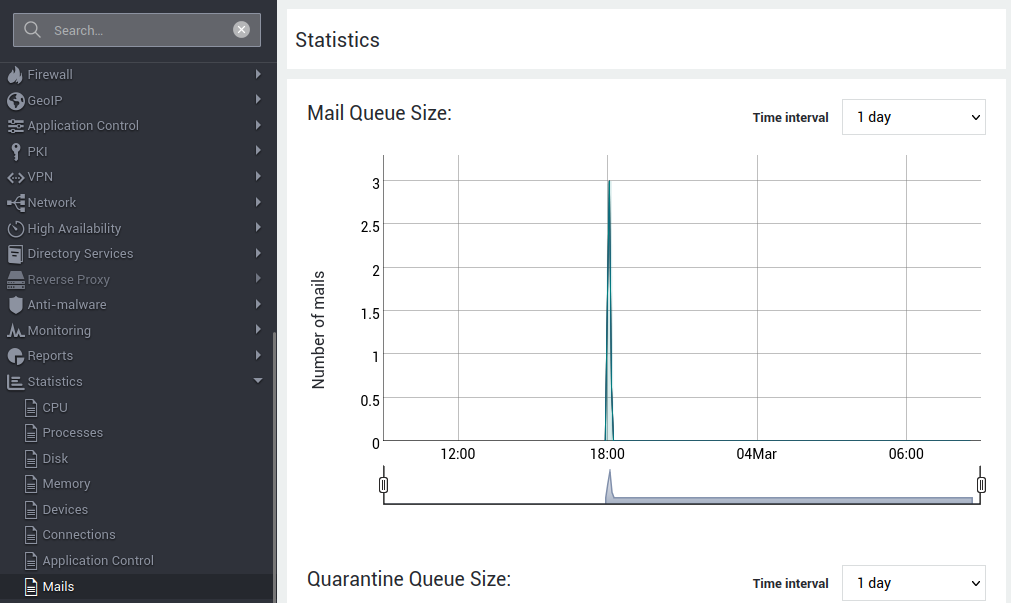
Mail Statistics¶
A new statistics page has been implemented, providing time-series data for key mail server metrics. This allows administrators to monitor performance and identify potential issues. The new statistics page offers insights into:
- Mail Queue size: Track the volume of emails waiting to be sent.
- Quarantine Queue size: Monitor the number of emails held for review.
- Mail Delay: Analyze the time it takes for emails to be delivered.
- Mail Status: Gain an overview of the mail server's operational status.
Improved DMARC Checking¶
DMARC (Domain-based Message Authentication, Reporting & Conformance) verification now influences the spam score of incoming emails. This significantly enhances spam detection accuracy and reduces the risk of phishing attacks.
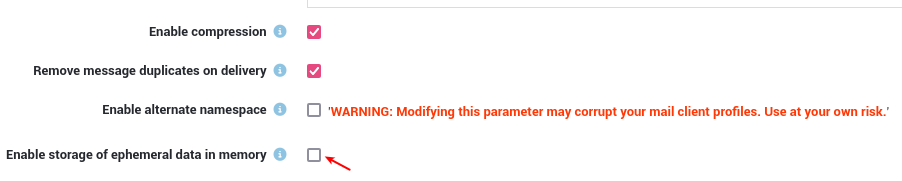
IMAP & POP Performance¶
To improve mail processing times, the I/O load on high-volume mail servers can be reduced by enabling additional RAM caches.
Additional Fixes¶
- Sorting on the "Mail Quota Status size" has been rectified.
- The mail size on the "Mail Queue size" page is now human-readable.
- When exporting the mail quota status page, the exported size is now in bytes instead of a human-readable string.
System Package Updates¶
Over 250 software packages have been updated to address security vulnerabilities and ensure the software remains current. These updates include bug fixes, performance improvements, and security patches, contributing to a more stable and secure system.
Discontinued Features¶
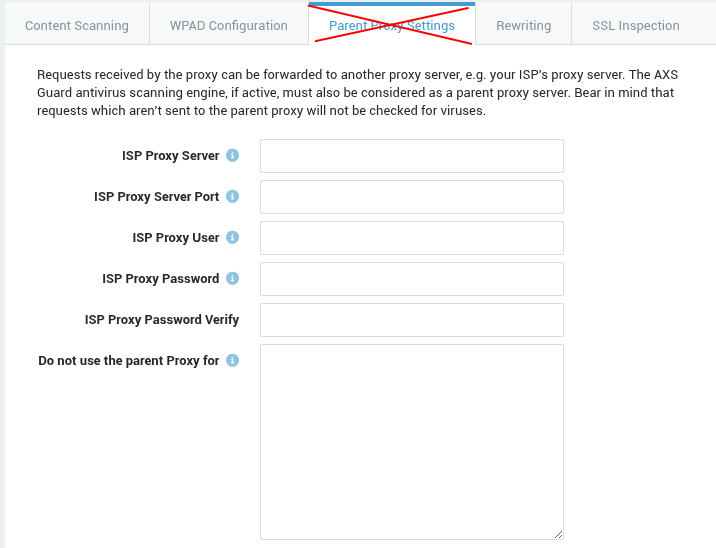
Parent Proxy for Web Access¶
Support for the Parent Proxy functionality has been discontinued.
Fax Module¶
Fax support has been completely removed. We recommend evaluating modern communication methods as a replacement for faxing.